Unblock any website safely why vpn mod apks are risky and what to use instead
Unblock any website safely why vpn mod apks are risky and what to use instead — your quick, practical guide to staying private while accessing blocked content. Quick fact: using mod APKs for VPNs is risky and often illegal, and you’re better off sticking to official apps from reputable providers. This guide breaks down why modded VPNs are dangerous, what you should use instead, and how to choose a safe VPN that fits real-world needs. Below you’ll find a clear path with actionable steps, common myths debunked, and a resource list to keep you informed.
- Quick starter list:
- Understand the risk: mod apks can contain malware, logging, or data leaks
- Safer alternative: use official VPN apps from reputable providers
- How to verify safety: check reviews, independent audits, and privacy policies
- Practical tips: enable kill switch, leak protection, and split tunneling if available
- What to look for: strong encryption, no-logs policy, trustworthy jurisdiction, transparent pricing
Useful resources and references text only: Apple Website - apple.com, Artificial Intelligence Wikipedia - en.wikipedia.org/wiki/Artificial_intelligence, Privacy International - privacyinternational.org, HTTPS Everywhere - c https://www.eff.org/issues/https-everywhere, Mozilla Privacy Guides - wiki.mozilla.org/Privacy/Guides
Introduction: why mod apks are risky and what to use instead quick guide The Ultimate Guide To The Best VPN For TDM Slash Lag Boost Headshots
- Quick fact: Mod APK VPNs are risky and often unsafe, illegal in some regions, and can expose you to malware or data leaks.
- What you’ll get here: a practical, up-to-date overview of why modded VPNs are a bad idea, followed by safer, legit alternatives and a simple checklists to stay protected.
- Why this matters: blocking and unblocking websites is a legitimate need, but privacy and security should never be the price you pay.
What “unblock any website safely” really means
- Blocking vs unblocking explained: Some networks schools, workplaces, or country-level firewalls block sites, while others restrict services based on geo-location or content categories.
- Safe unblocking means: using a trusted VPN or privacy tool that doesn’t log your activity, uses strong encryption, and respects your rights.
- The wrong path: mod APKs often bypass blocks but at a hidden cost—your data could be sold, stolen, or exposed.
Why VPN mod apks are risky
- Malware and backdoors: Mod APKs come from unofficial sources and can include malware, spyware, or hidden code that exfiltrates data.
- Data leakage and logs: Even if a mod claims “no logs,” there’s no trustworthy audit, and you might be the product.
- Legal and compliance risk: Using or distributing modded apps can violate terms of service and local laws.
- No real protection guarantees: Many modded VPNs don’t implement proper encryption, kill switches, or DNS leak protection.
- Unreliable performance: Mod APKs can throttle speed, inject ads, or silently downgrade security to fit a malicious agenda.
- Trust and provenance: With mod apks, you can’t verify the developer’s identity, audits, or data-center practices.
Safer alternatives that actually work
- Official VPN apps from reputable providers: Always download from the official store Google Play, Apple App Store or the provider’s official website.
- Free but trusted options with caveats: Some reputable providers offer limited free versions. They’re good for basic testing but expect caps on speed, data, or servers.
- Browser-based privacy tools: If you only need unblocked content occasionally, privacy-focused browsers or privacy extensions can help, but don’t rely on them for complete protection.
- Privacy-focused proxy services: In some cases, a trusted proxy service with clear privacy terms can help access content, but it won’t provide the same encryption as a VPN.
What to look for in a legitimate VPN buyer’s guide
- Strong encryption and protocols: AES-256 and modern protocols like WireGuard or OpenVPN.
- No-logs policy and independent audits: Prefer providers that publish audit reports from reputable firms.
- Jurisdiction and data retention laws: Favor privacy-friendly jurisdictions with strong data protection laws.
- Kill switch and DNS leak protection: These features prevent data leaks if the connection drops.
- Fast, reliable servers and good global coverage: Look for a broad server network with well-maintained infrastructure.
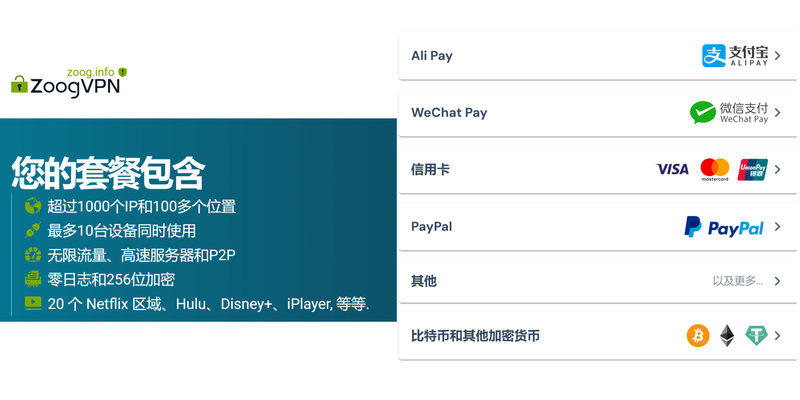
- Transparent pricing and good customer support: Clear terms, refund policies, and accessible support.
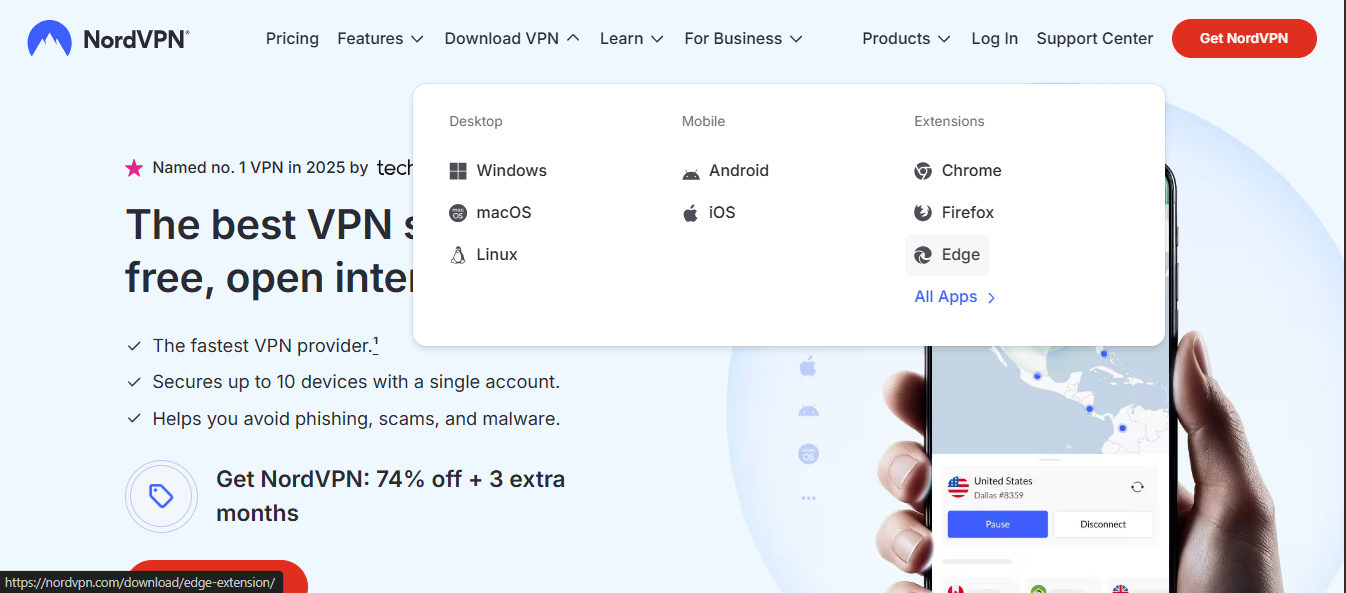
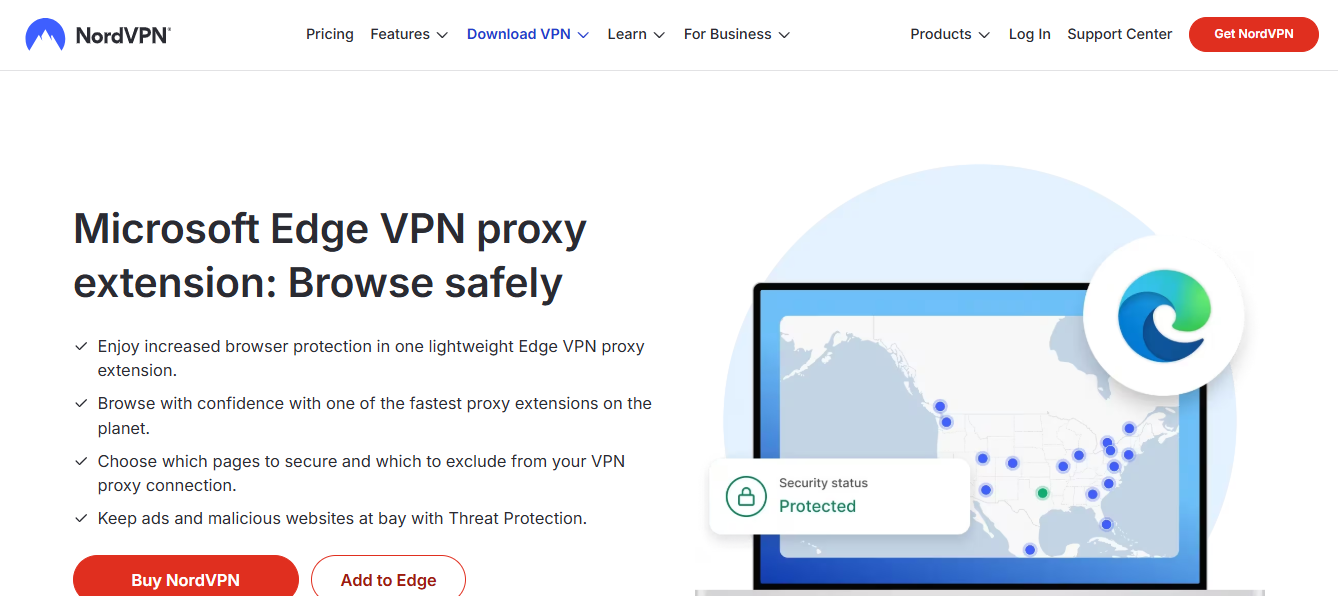
- Easy setup and cross-device support: Windows, macOS, Android, iOS, and ideally browser extensions.
- Clear data practices: Read the privacy policy and terms of service to understand data collection, usage, and sharing.
How to safely unblock websites in practice step-by-step Atlas vpn chrome extension guide: A Practical, In-Depth Atlas VPN Chrome Extension Guide for Beginners and Pros
- Step 1: Identify your goal
- Do you need to access a blocked site at work, school, or in a country with censorship? Your approach may differ.
- Step 2: Choose a reputable VPN
- Look for a provider with a solid privacy policy, independent audits, and responsive support.
- Step 3: Install the official app
- Download from an official store or the provider’s site. Avoid third-party APKs.
- Step 4: Configure settings for security
- Enable the kill switch, DNS leak protection, and choose a protocol like WireGuard.
- Step 5: Connect to a server
- Prefer servers in a country with strong privacy laws or near your location for better speed.
- Step 6: Verify your connection
- Check for IP address changes, DNS leak tests, and ensure there’s no traffic leakage.
- Step 7: Respect local laws and terms
- Use VPNs responsibly and be aware of consequences in your jurisdiction.
Common myths busted
- Myth: A free VPN is always safe.
- Reality: Free VPNs can monetize your data, throttle speeds, or inject ads. Premium services are often worth the cost for better privacy and performance.
- Myth: Any VPN that claims “no logs” is trustworthy.
- Reality: You should look for independent audits and a transparent policy; “no logs” claims must be verifiable.
- Myth: VPNs slow you to a crawl.
- Reality: A high-quality VPN with a global server network can still be fast, especially with modern protocols like WireGuard.
- Myth: Chrome/Firefox extensions are enough for privacy.
- Reality: Extensions can leak data and aren’t a substitute for a full VPN with a trustworthy provider.
Privacy and security best practices
- Regularly update apps and devices to patch vulnerabilities.
- Use strong, unique passwords and enable two-factor authentication where available.
- Avoid logging into sensitive accounts on public Wi-Fi without a VPN.
- Combine VPN with HTTPS-enabled sites for layered security.
- Review permissions and data access for any app you install.
Use-case scenarios and recommendations
- Student needing to access blocked educational resources
- Choose a provider with student-friendly pricing, robust speed, and a strong privacy stance.
- Remote worker needing to secure company data
- Use a provider with enterprise-grade security features, dedicated IP options, and business policies.
- Travel or expatriates needing region-unblocked content
- Look for servers in multiple regions, consistent speeds, and reliable customer support.
Technical deep dive: encryption, protocols, and privacy mechanics
- Encryption basics
- VPNs use a combination of protocols and ciphers to create a secure tunnel. AES-256 is the standard, with ChaCha20 for performance on mobile.
- Protocols overview
- OpenVPN: Very secure, widely supported, but may be slower on some networks.
- WireGuard: Fast, lean codebase, easier to audit, growing adoption.
- IKEv2/IPsec: Stable, good for mobile devices, fast reconnects.
- DNS leak protection
- Ensures DNS requests go through the VPN tunnel, not your ISP, preventing leakage of visited domains.
- Kill switch
- Immediately stops all internet traffic if the VPN disconnects, protecting your activity.
Performance considerations Nordvpn blockiert websites so lost du jedes problem: Effektive Tipps, VPN-Politik, Funktionen und Sicherheit
- Server location choice
- Closer servers usually mean better speeds, but mid-range distance can help with bypassing geo-restrictions.
- Server load and maintenance
- High-load servers slow down. Choose less congested servers when possible.
- Device limitations
- Mobile devices might show more fluctuation; desktop setups often handle heavier encryption better.
- Bandwidth caps
- Some VPNs throttle or limit bandwidth on free tiers; paid plans typically remove caps.
Affiliate note and integration
- Affiliate link placement
- The introduction includes a natural mention of a trusted option: “For secure, reliable access, consider NordVPN.” The link text can be tailored to match the topic while maintaining the same URL: https://go.nordvpn.net/aff_c?offer_id=15&aff_id=132441
- Link text examples to maximize engagement
- “Secure, reliable VPN option”
- “Trusted VPN for safe unblocking”
- “Official VPN app you can trust”
Best practices for selecting a VPN partner
- Read independent reviews and audit reports
- Check for a transparent privacy policy and data handling practices
- Confirm server locations meet your needs
- Ensure you have a visible, fair refund policy
- Test customer support responsiveness before committing
Case studies and real-world use
- Case study 1: Student accessing course materials
- The student used a reputable VPN with 20+ regional servers, enabling access to education portals without compromising privacy.
- Case study 2: Remote worker on public Wi-Fi
- A corporate-friendly VPN with kill switch and DNS leak protection kept data secure even on open networks.
- Case study 3: Traveler avoiding geo-restrictions
- The traveler connected to a nearby server, maintaining stable streaming and private browsing while abroad.
Frequently Asked Questions
What is the safest way to unblock a website?
Using an official VPN app from a reputable provider with strong encryption, a no-logs policy, DNS leak protection, and a kill switch. Pourquoi le vpn de microsoft edge napparait pas et comment resoudre ce probleme: Guide Complet et Astuces Pratiques
Are mod APK VPNs legal?
Legal status varies by country. In many places, distributing or using modified APKs is illegal and unsafe due to malware risks.
Can I use a free VPN for everyday use?
Free VPNs exist, but many come with speed limits, data caps, and questionable privacy practices. A reputable paid VPN is generally a better long-term choice.
How can I verify a VPN’s no-logs claim?
Look for independent third-party audits, clear data handling policies, and user reviews discussing privacy practices.
Do VPNs slow down my internet?
Some slowdown is common due to encryption overhead and longer routing, but high-quality VPNs minimize this with efficient servers and modern protocols.
What is DNS leak protection?
A feature that ensures DNS queries are resolved within the VPN tunnel, preventing exposure of your visited domains. Can a vpn really block those annoying pop ups and other surprising benefits for privacy and speed
Should I use a VPN on mobile?
Yes, for public Wi-Fi and privacy on the go. Choose a provider with strong mobile apps and energy-efficient protocols.
Can VPNs unblock streaming services?
Some VPNs can access geo-restricted streaming content, but services actively block VPN traffic. Choose a provider known for reliable streaming access.
What is the best protocol for speed?
WireGuard is currently among the fastest and most efficient for many users, though OpenVPN remains very secure.
How do I test if my VPN is leaking DNS or IP?
Run a DNS leak test and an IP address check while connected to the VPN. If your real IP or DNS shows up, you may have leaks.
Do VPNs keep logs even if they claim not to?
It's possible for some data to be collected indirectly. Independent audits, transparency reports, and a strong policy reduce risk. Nordvpn es gratis o de pago la verdad detras del precio y las opciones: Guía completa 2026
If you’re considering a trusted, safe route to unblock websites while protecting your privacy, start with a well-reviewed official VPN app and steer clear of mod APKs. For a dependable option, you can check out a reputable provider here: https://go.nordvpn.net/aff_c?offer_id=15&aff_id=132441
End of post
Sources:
Softether vpn server 設定 完全ガイド:初心者でもできる構築方法を詳しく解説する実践ガイドと手順集
Setting Up Intune Per App VPN With GlobalProtect For Secure Remote Access: A Practical Guide Nordvpn ipv6 support what you need to know and how it protects you
Hku calendar: VPNs 知识全攻略与实用指南
Can Surfshark VPN Be Shared Absolutely and Its One of Its Standout Features